Even if you use end-to-end encrypted messaging and delete the app entirely, your “private” conversations might not be as gone as you think. Recent legal proceedings have revealed a significant security loophole: iPhone notification databases can store fragments of messages long after the sending app has been uninstalled.
The Texas Case: A Privacy Breach in Court
The vulnerability came to light during the trial of nine individuals charged with domestic terrorism following a July 2025 incident at the ICE Prairieland Detention Facility in Texas. During the proceedings, it was revealed that the FBI successfully extracted private Signal messages from an iPhone used by one of the defendants.
The implications of this testimony are striking:
– The App Was Gone: An FBI special agent testified that the Signal app had already been deleted from the device at the time of forensic examination.
– Disappearing Messages Failed: Despite the use of Signal’s “disappearing messages” feature, the content remained accessible.
– The Source of the Leak: While Signal successfully deleted the message within its own encrypted environment, the iPhone’s notification system had already cached the text in its internal database.
Why This Matters: The Notification Loophole
This discovery highlights a critical disconnect between secure app development and mobile operating system behavior. Signal is designed to ensure that once a message is gone, it is gone. However, when a message arrives, the smartphone’s operating system (iOS) often creates a secondary record to display a push notification on your lock screen.
In this instance, the FBI did not “break” Signal’s encryption; rather, they bypassed it by retrieving the “shadow” copies of the messages left behind by the iPhone’s notification management system.
“Someone who deletes a secure messaging app reasonably expects that their messages won’t hang around indefinitely or be retrievable if the device falls into untrusted hands,” says John Davisson, deputy director of the Electronic Privacy Information Center.
This raises a fundamental question for digital privacy: Can an app truly be considered secure if the operating system beneath it is leaking its data?
How to Secure Your Messages
If you rely on Signal for high-stakes privacy, you cannot assume that deleting the app is sufficient. To prevent your messages from being archived in the iPhone’s notification database, you must change how the app interacts with your phone’s lock screen.
Step-by-Step Privacy Guide
To ensure your messages do not leave a digital footprint in your phone’s system logs, follow these steps on both iOS and Android :
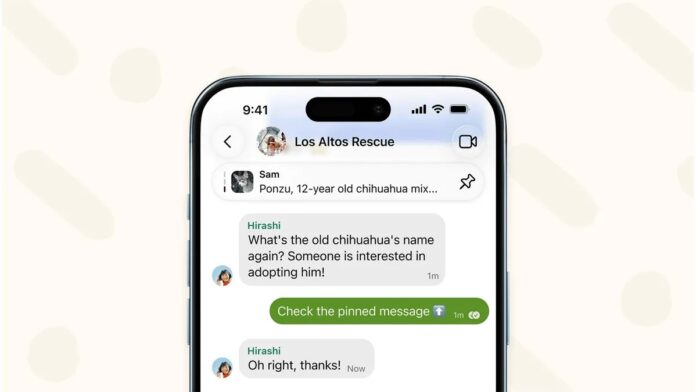
- Open Signal and go to the Settings menu.
- Select Notifications.
- Locate the setting for “Show” (or “Show Preview”).
- Change the setting to “No name or message.”
The Result: You will still receive push notifications letting you know you have a new message, but the notification will be blank. It will not display the sender’s name or the message content. While this requires the extra step of opening the app to read every text, it ensures that no readable data is stored in the iPhone’s internal storage, making forensic extraction much more difficult.
Conclusion: Digital privacy is a layered defense; even the strongest encryption can be undermined by how your smartphone handles notifications. To maintain true anonymity, users must configure their apps to prevent the operating system from caching sensitive information.